Named as a pun on Microsoft BackOffice Server software, Back Orifice 2000 (BO2k) has been designed as remote administration tool. The nefarious tool has its origins in the Defcon computer security convention.
It is based on a plug-in architecture, which allow expanding its functionality to new horizons, and it is regarded as a malicious application because installing it can be done by an unauthorized user.
In order to keep users safe from falling under the control of a remote user, some developers came up with specifically designed removal tools.
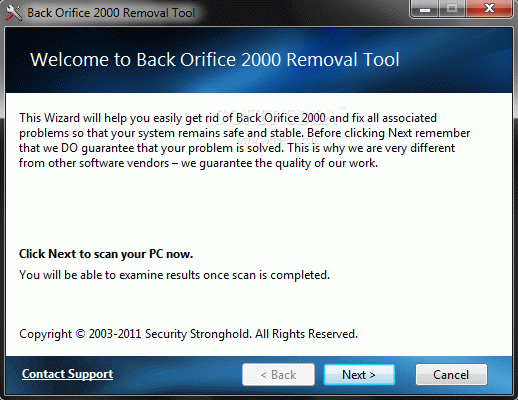
There is no need to guess what Back Orifice 2000 Removal Tool has been designed for, as the name lays the purpose out in the open.
Installing the utility is a simple task that completes with little effort from the user. However, attention to the process is required because it attempts to add unnecessary third-party tools to the system.
The interface is straightforward and does not leave any room for confusion: simply initiate the system scan procedure and wait for the finish.
The removal tool is designed to find all the traces of BO2k and eliminate them; this includes malicious processes and registry entries. Moreover, the developer touts that it can decrease the chances of the remote administration tool to ever lodge into the system again.
Apart from “search and destroy” capabilities, BO2k Removal Tool also features the possibility to reset to default the configuration of certain web browsers.
BO2k Removal Tool is not complicated and it incorporates the necessary routines to get rid of the targeted data. Its advantage is that it knows exactly where and what to look for.
On the other hand, BO2k has not been updated in a long time and it is very likely that the security settings in the modern operating systems trigger an alert before anything happens.
Umberto
спасибо, работает)
Reply
Monica
awesome Back Orifice 2000 Removal Tool crack
Reply
Davide
спасибі за кряк для Back Orifice 2000 Removal Tool
Reply
josue
salamat sa inyo para sa keygen Back Orifice 2000 Removal Tool
Reply