Developers who handle large volumes of information with different sensitivity statuses could be requiring a way of protecting their codes. Obfuscator was created precisely for that purpose and it will enable those who write assembler codes to protect their data from decompilation and reverse engineering.
It will allow users to make their assembler code difficult to analyze and therefore prevent any cracking attempts over their data. Being provided both as an executable file or archive, the application’s deployment package will also include several examples that will help novice users familiarize with its handling and offered features.
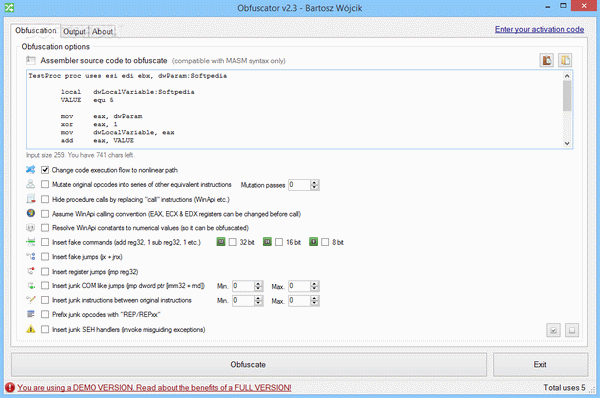
Using its bundle of tools, people will be able to change the execution flow, in order to prevent debugging, by increasing the complexity of the code, which in turn results in a more difficult analysis. Furthermore, the original code instructions can be mutated, into series of equivalent opcodes and the application offers users the choice of moving both arithmetic and logical ones.
The obfuscation process will also enable users to hide direct API call functions, insert garbage opcodes in the real code, in order to induce scatter noise or insert fake instructions. Fake exceptions are also supported and WinAPI constants can be resolved to numerical values in order to facilitate the obfuscation process.
Experienced users could benefit from the fact that the application offers recognition of “db”, “dw”, “dd”, “dq” data declarations between the instructions. In the online documentation one will be able to find access to numerous command and function descriptions that are aimed at helping people get a grasp on the required syntax.
John
Baie dankie vir die serial Obfuscator
Reply
Piero
спасибо за кряк для Obfuscator
Reply
John
thanks for the patch for Obfuscator
Reply
Cristina
Baie dankie vir die keygen
Reply