We all know the Internet is a safe haven for all sorts of malicious content lying around, if not openly trying to make as many victims as possible.
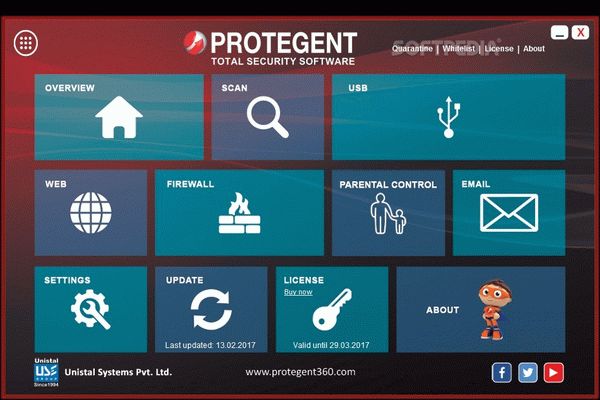
While this depiction of the online universe might seem quite grim, there are software solutions that can protect you from suspicious content while surfing the web, thus guaranteeing a flawless experience. Protegent Total Security is one of the said software utilities that bundle a multitude of handy tools.
First of all, you need to know that Protegent Total Security includes two different modules, one bearing the same name as the full-featured product, and the other called Crash Proof.
Being a comprehensive Internet protection tool, Protegent Total Security incorporates a multitude of features letting you scan your computer in order to spot any kind of risk, from malware and spyware to code emulations, and more, with the possibility of relying on real-time detection as well.
As for the “Web” section, it offers to monitor any of the following themes: unethical (aggressive, malware, phishing, spyware, violence), adult and controversial (sexuality, drugs, guns), computers & internet (ads, social networks, mail, chat), business interests (financial, marketingware), personal interests (games, gambling, celebrity).
Plus, resorting to the parental control features should enable you to restrict your children’s access to specific topics that you may find damaging to their education. Then, Mail Protection is another highlight that should ensure your data is by no means not collected.
We have mentioned Crash Proof in the beginning as being a complementary piece of software that can prove useful in situations involving accidentally deleted, lost, or damaged data, with the program being able to recover it all. Data loss prevention settings are bundled so that automatic tasks are performed regularly in this respect.
All in all, Protegent Total Security is an all-encompassing collection of tools that can keep you safe while online since it can address any kind of threat while also letting you restrict the content that reaches your computer. The security levels it guarantees should be considerable and complemented by the recovery tools it also puts at your disposal.
kaue
спасибі за патч для Protegent Total Security
Reply
John
Tack för Protegent Total Security seriell
Reply