The range of threats that can affect a computer when navigating online should be enough to put PC users on guard and have them install reliable security software onto their systems. Total Defense Internet Security Suite is one of the tools that promises to prevent malware from infecting the PC, protecting it from viruses, spyware, spam and more.
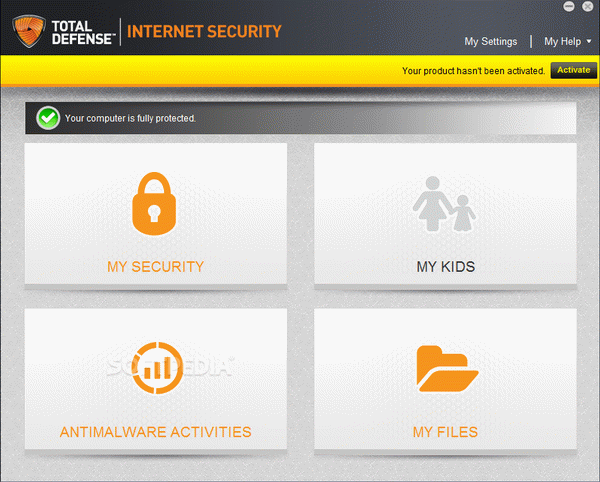
This security tool includes an anti-virus module that can perform full, quick or custom scans in order to detect possible infections and send the malicious files to quarantine. It is advisable that you perform regular scans in order to ensure that the system is secure at all times.
The built-in personal firewall aims to automatically restrict network activity that is identified as dangerous. You can assign connection to certain zones (home, public etc.) to categorize them as trustful and configure your own rules, which offers you the possibility to choose the connections to block and the ones to allow. Access profiles can be created in order to assign certain rules to multiple IP addresses and create schedules for activating rule sets.
The application can block cookies and annoying popup windows and comes with cache cleaning functionality. The identity theft protection module allows you to get a warning before private information is sent to a website and protect your privacy.
The suite bundles spam protection and can identify phishing endeavors. It is capable of memorizing all the inbound and outbound connections, allowing you to view the access attempts.
The parental control module is intended to give a helping hand to parents who want to protect their children from inappropriate content or specific websites, restrict access to the Internet during the day or block certain applications (for instance, instant messaging or peer-to-peer transfers).
Real-time file and email scanning, cloud protection and registry security are features that recommend Total Defense Internet Security Suite as a tool that can safeguard your PC without interfering with your daily work. It is intended to help you eliminate the items that put your computer and private data at risk, giving you the freedom to customize data access policies.
Paolo
the great work
Reply
Paolo
salamat sa inyo para sa serial
Reply
tom
Gracias por Total Defense Internet Security Suite serial
Reply
Francesca
salamat sa inyo para sa keygen Total Defense Internet Security Suite
Reply